In many organizations, visitor management is still not taken seriously with little or no record keeping. Visitors and contractors may be asked to sign a paper visitor log, or worse, nothing at all. While this is cheap and easy, it provides very little security or risk management, and poses a number of other significant problems. Call us today to discuss how simple it is to upgrade your visitor management process.
Risks and Challenges of many Visitor Management systems:
- More often than not, the names are incomplete and not legible.
- It is easy (and unfortunately too common) for the names to be false.
- Check in/out times are not always verified, required or enforced.
- In cases of emergency (fire, earthquake, flood, etc), it is very difficult to determine who is still in the building quickly during the stressful situation.
- In cases of security breaches (theft, threats, etc), it is difficult to positively identify who was in the facility during a specific period of time (people with malicious intent are more likely to falsify information).
- Information regarding the identity of visitors is readily available for everyone to see, but this information should be private and confidential.
- Visitor badge systems are effective only if a policy and culture of enforcement exists, where all authorized persons must display a badge (absence gets noticed).
- Hand-written visitor badges or business cards in pouches are easily duplicated.
- Paper logs and hand-written visitor badges present a perception of lax security and an unprofessional image to visitors. Overly-complicated and time-consuming security measures may, however, appear unwelcoming to legitimate guests.
- Doing nothing is completely unhelpful to law enforcement, may be contrary to regulations for your industry or in the jurisdiction where you operate, and may even compromise your ability to make claims through your insurance coverage.
How to improve your current Visitor Management system:
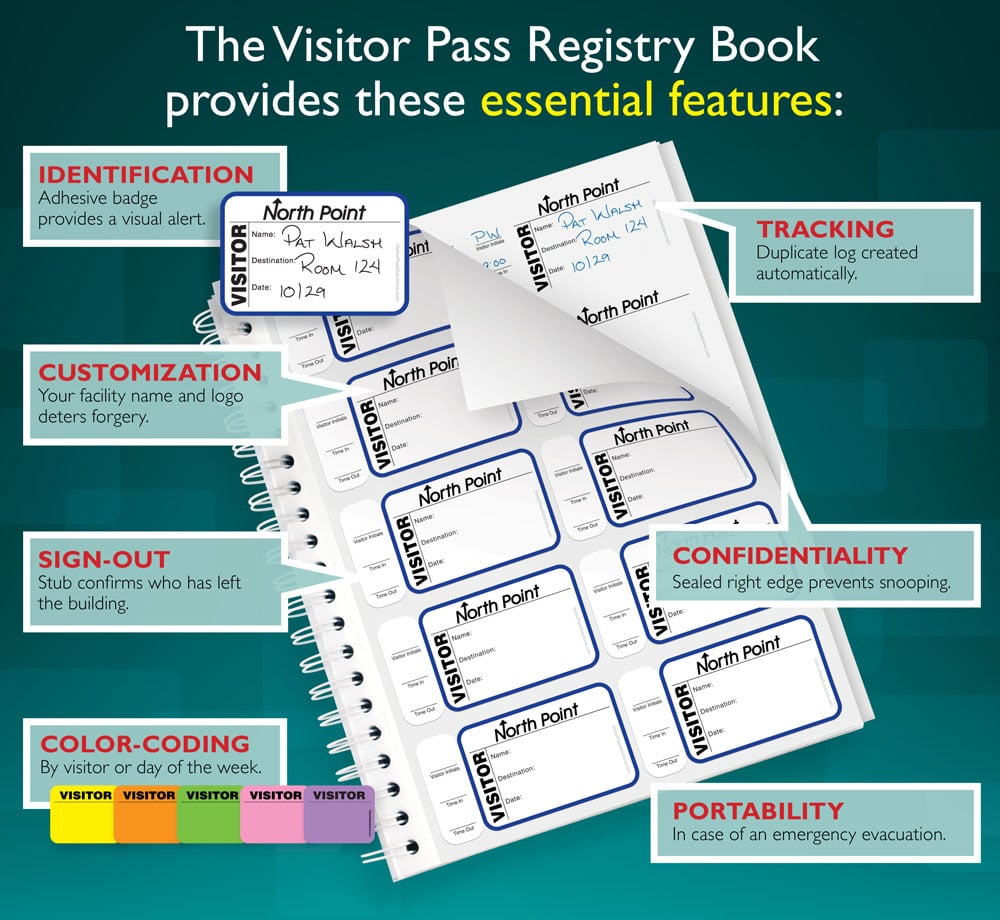
To address the issues listed above, organizations should, at the very least, ensure that receptionists, front-desk and security personnel verify the identity, date & time, purpose of visit, and entrance/exit for each visitor through their point-of-entry. To assist in visitor management and privacy, many organizations (regardless of size) are implementing better log book options, expiring visitor badges, or even IT-based visitor management systems such as Passage Point or Easy Lobby.
Electronic Visitor Management solutions offer the following benefits:
- Securing the workplace more robustly
- Streamlining the visitor check-in process
- Capturing detailed visitor information more accurately and automatically
- Being able to easily perform analysis and reporting on visitor data and manage multiple locations
- Keeping visitor and company information confidential
- Providing high quality, professional looking badges to visitors and employees
- Enhancing the organization’s image and making visitors and employees feel safer
- Being able to tightly integrate the visitor system with your access control system to further improve security
These systems reside on a computer (terminal or mobile device) available at the reception desk and/or other physical points of entry. They effectively, efficiently and securely automate the process of registering visitors and printing badges or other types of identification. Depending on the requirements of your security policy, site survey and risk assessment, you could choose from a variety of solutions.
These software programs are usually easy to learn, easy to use, and depending on their complexity, relatively easy to install. Visitor management becomes a fast and easy process with the following steps:
- Capture or Enter information, as needed upon entrance or exit to facility
- Enter any required information. Depending on the complexity and cost of your system, you may have hardware or software to automate these processes. (i.e.: Driver’s License and Business Card Scanners, Cameras, Signature Capture Pads, Bar Code Readers, Web Pre-registration, etc)
- Enter additional information such as the Category of visitor, name of the person being visited, and reason for the visit (usually presented as drop down lists to choose from).
- Print/Issue a customized Visitor Badge (or revoke upon person exiting facility)
- When you print, the software usually records the time and date, and prints a badge based on the template selected (Badges can look different for different groups: Employees, Visitors, Students, Contractors, etc). Many software versions come with pre-designed badge templates, as well as badge designer software to make your badges uniquely identifiable. You then print to any Windows-based printer (black and white thermal label printer, inkjet, laser, or PVC card printer).
- Depending on your printer, you can even use self-expiring badge stock or labels, which bleed through after a specified time to show the badge has expired. Printing a barcode on the temporary badge allows for scanning of the badge to make check-out very quick (with the appropriate hardware).
- More complex systems can be integrated with popular Access Control systems allowing you to grant visitors temporary card access (Prox/Mag stripe/SmartChip, etc) directly from the visitor management software.
- Data Analysis and Reporting
- In case of emergency or threat, you can instantly and automatically create a report of individuals known to be at your location at that exact time. For normal analysis or other business reasons, you can look up and sort visitor data and visit information by a variety of criteria.
Security should be a top priority for any organization that gets visitors to its facilities, regardless of size. In addition to keeping better track of who is in your buildings and why, companies can also present a more security-conscious and professional image to all of their visitors, contractors, partners, and prospective employees. With a secure visitor management system, visitors feel like they are in a professionally managed, more secure facility, and both employees and visitors feel safer.